Anna Bacher
How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
#1about 5 minutes
Understanding the IDOR vulnerability and its impact
IDOR (Insecure Direct Object Reference) is an OWASP Top 10 vulnerability that can lead to data leaks, account takeovers, and system crashes.
#2about 3 minutes
How a simple IDOR flaw caused a massive data breach
The First American Financial Corporation breach leaked 885 million documents because attackers could simply change a number in a URL to access unauthorized files.
#3about 15 minutes
A practical demonstration of exploiting IDOR vulnerabilities
Using Burp Suite and OWASP Juice Shop, an attacker can intercept requests to change basket IDs or modify other users' product reviews.
#4about 3 minutes
Examining IDOR vulnerabilities in major companies
Real-world examples from HackerOne show how IDOR vulnerabilities in companies like PayPal and Starbucks can lead to account takeovers and payment data exposure.
#5about 10 minutes
Why IDOR is difficult to prevent and tools that can help
Preventing IDOR is challenging because it requires manual access control checks, but tools like Code Property Graphs (CPG) and GitHub's CodeQL can help automate detection.
#6about 5 minutes
Using neural networks for advanced IDOR detection
By combining Code Property Graphs with neural networks, it's possible to detect IDOR vulnerabilities with higher accuracy and even generate automated code fixes.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
02:15 MIN
Preventing broken object level authorization vulnerabilities
Bullet-Proof APIs: The OWASP API Security Top Ten
Unlock full access
Log in or set up an account to access this feature and more.

02:39 MIN
Focusing on key OWASP Top 10 risks for developers
Delay the AI Overlords: How OAuth and OpenFGA Can Keep Your AI Agents from Going Rogue
Unlock full access
Log in or set up an account to access this feature and more.
03:27 MIN
Common security failures beyond individual coding errors
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock full access
Log in or set up an account to access this feature and more.

02:52 MIN
Common web application threats like injection and DoS
Security in modern Web Applications - OWASP to the rescue!
Unlock full access
Log in or set up an account to access this feature and more.

02:26 MIN
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock full access
Log in or set up an account to access this feature and more.

04:54 MIN
Why developers are a prime target for attackers
You click, you lose: a practical look at VSCode's security
Unlock full access
Log in or set up an account to access this feature and more.
04:01 MIN
Focusing on the top three OWASP security threats
It's a (testing) trap! - Common testing pitfalls and how to solve them
Unlock full access
Log in or set up an account to access this feature and more.

04:38 MIN
Hands-on security training for developers
How GitHub secures open source
Unlock full access
Log in or set up an account to access this feature and more.
Featured Partners
Related Videos
 2:08:06
2:08:06The attacker's footprint
Antonio de Mello & Amine Abed
 43:56
43:56Getting under the skin: The Social Engineering techniques
Mauro Verderosa
 44:30
44:30Securing Your Web Application Pipeline From Intruders
Milecia McGregor
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 37:36
37:36Walking into the era of Supply Chain Risks
Vandana Verma
 27:32
27:32Security Pitfalls for Software Engineers
Jasmin Azemović
 58:19
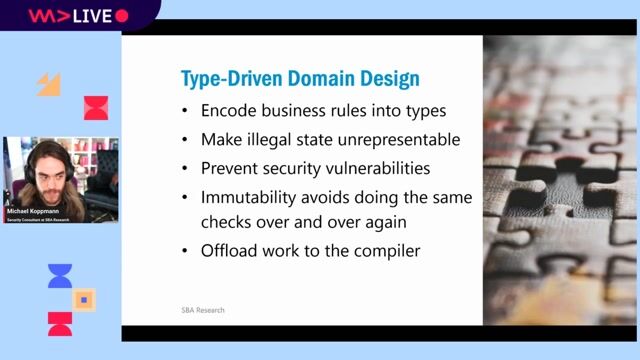
58:19Typed Security: Preventing Vulnerabilities By Design
Michael Koppmann
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.


Codasip
Berlin, Germany


INFODAS Gesellschaft für Systementwicklung und Informationsverarbeitung mbH
Remote
Linux

Koda Staff




Vesterling Consulting GmbH
€70-90K
Software Architecture